IT OT convergence is the integration of traditional enterprise IT systems with operational technology (OT) so organizations can monitor and control physical devices and processes alongside business systems.
In practice, it bridges the world of ‘bits and bytes’, combining identity, email, cloud, endpoints and servers, with industrial pumps and valves, controllers, sensors, building automation, medical imaging systems and other cyber‑physical equipment.
Many treat convergence as a connectivity project. ISC2’s perspective is broader: IT OT convergence is a governance and workforce evolution. When IT and OT merge, risk ownership changes, decision-making must align across safety and security priorities, and teams need shared language and validated skills.
This guide explains why convergence is accelerating, the benefits of IT/OT convergence, the most common IT/OT convergence security challenges, and a practical strategy for leaders who must secure modern, interconnected environments.
The Expanding Scope of IT OT Convergence
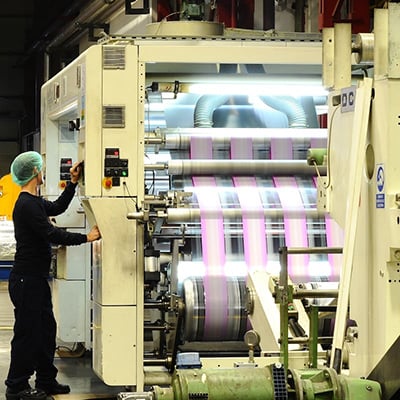
IT OT convergence in manufacturing is the most familiar use case: production lines, robotics and industrial sensors are increasingly connected to enterprise networks so operations teams can optimize throughput, quality and uptime.
But convergence is now a cross‑sector reality wherever cyber systems touch physical outcomes. That includes healthcare (connected medical devices and imaging systems), smart buildings (HVAC, lighting and physical access control), transportation (fleet and infrastructure telemetry) and critical infrastructure (utilities and energy).
As the scope expands, so does the need for consistent risk management: leaders must understand what is connected, who owns it, which pathways exist between IT and OT, and what failure would mean for safety, service continuity and regulatory obligations.
See also: Deep Dive: OT Security Challenges
The benefits of IT/OT convergence for modern enterprises
The benefits of IT/OT convergence typically come from improved data flow between operations and business systems. Common drivers include:
- Real‑time visibility: consolidated dashboards that show performance, utilization and anomalies across sites and assets.
- Predictive maintenance: analytics on sensor data to identify failure patterns early, reducing downtime and extending asset life.
- Lower operational costs: fewer unplanned outages, better scheduling, and more efficient resource use.
- Faster decision‑making: operational insights can inform supply chain, quality and safety decisions without manual reporting delays.
- Innovation enablement: convergence supports new models such as remote operations, digital twins and smart facilities.
Historically, many OT environments were designed as ‘air‑gapped’ or isolated because remote connectivity was limited and cybersecurity risk was less understood. Today, IP networking, web interfaces and APIs are more common in OT management components, making integration easier, but also raising the stakes for security and governance.
Navigating IT/OT Convergence Security Challenges
IT/OT convergence security challenges arise because OT systems were not designed to inherit the same rapid change cadence as enterprise IT. In OT, stability and safety often outweigh speed, and even routine security actions, patching, scanning, deploying agents, may require vendor approval or scheduled downtime.
Convergence can also amplify risk pathways. A compromise that starts in IT, such as stolen credentials from phishing, can become an operational incident if network segmentation and access controls allow an attacker to pivot toward OT management interfaces. In cyber‑physical environments, that can translate into production disruption, service outages, or safety impacts.
To secure converged environments, leaders should assume that not every OT asset can accept standard endpoint tooling. Security design often has to rely more on architecture controls (segmentation, restricted pathways, strong identity) and careful monitoring at boundaries and choke points.
Common IT/OT convergence security challenges include:
- Legacy system vulnerabilities (long lifecycles, older firmware/OS dependencies, vendor constraints)
- Difficulty of traditional patching cycles (maintenance windows, validation requirements, operational approvals)
- Protocol incompatibilities (specialized industrial protocols and visibility gaps)
- Expanded attack surfaces (more endpoints, remote access, shared identity paths)
- Tooling limitations (security agents, vulnerability scanning and EDR may be impractical on some OT assets)
Related learning: Course: Protecting Data Using Zero Trust
Bridging the governance gap: safety vs. security
A frequent obstacle in IT OT convergence is not technology, it’s governance. IT security teams often prioritize confidentiality and rapid remediation; OT teams prioritize availability, safety and controlled change. Both are rational, but they can conflict if there isn’t a shared decision framework.
A unified IT OT convergence strategy clarifies how the organization balances safety, uptime and information security. It defines what ‘critical’ means (safety impact, operational impact, regulatory impact), who can approve changes, how exceptions are handled, and what minimum controls apply across zones.
Effective governance also improves procurement and lifecycle management. When IT and OT stakeholders collaborate early, security requirements, like secure remote access, logging, and supportability, can be built into purchasing decisions instead of bolted on after deployment.
Closing the Skills Gap: Workforce Implications of Convergence
The most underestimated barrier to successful IT OT convergence is the skills gap. Many cybersecurity professionals are fluent in IT controls but unfamiliar with OT realities such as programmable logic controllers (PLCs), safety systems, vendor maintenance models and downtime constraints.
At the same time, many operations engineers are experts in physical processes but have had limited exposure to identity risks, threat modeling, incident response, or modern governance expectations. Convergence requires professionals who can translate across both worlds.
A practical way to close this gap is to build blended teams and adopt training pathways that validate knowledge in governance, risk and hands‑on security operations.
Explore pathways: Explore ISC2 Certifications
Scaling excellence through certified teams
Converged environments benefit from role diversity: leaders who can align stakeholders and risk appetite, and practitioners who can implement controls and run day‑to‑day security operations.
Organizations often pair governance-oriented capability with operational security capability to ensure the converged estate is managed by people who understand both languages, business risk and operational constraints.
To scale this model across sites, many organizations use structured enablement programs that upskill existing industrial staff while aligning enterprise security teams on OT-aware practices.
For organizational training at scale: Enterprise Solutions
A Proactive IT OT Convergence Strategy
Below is a leader-friendly roadmap you can adapt whether you’re a CISO, IT director, plant manager, or facilities leader. The goal is intentional connectivity with controls designed for cyber‑physical risk:
- Comprehensive asset discovery: Build a living inventory of IT and OT assets, including ownership, connectivity, criticality, vendor constraints and maintenance windows.
- Zero Trust micro‑segmentation: Segment networks by function and criticality. Restrict pathways between IT and OT to only what is required, and protect management planes with strong access controls.
- Unified governance framework: Define shared policies for change control, risk acceptance, access approvals and procurement requirements that apply across IT and OT.
- Continuous monitoring and threat detection: Increase visibility at boundaries and choke points. Use logs, network telemetry and anomaly detection approaches that respect OT performance constraints.
- Incident response testing: Run tabletop exercises and simulations that include operations, safety, IT security, legal and leadership because convergence incidents are rarely ‘just cyber.’
Master IT/OT Convergence with a Certified Workforce
Successful IT OT convergence is a long-term capability, not a one-time integration project. The benefits of IT/OT convergence, predictive maintenance, operational visibility and faster decisions, are only realized when IT/OT convergence security challenges are addressed with durable governance, tested processes and skilled people.
Leaders who invest in cross-functional training and globally recognized standards can reduce friction between teams, improve audit readiness, and create consistent security outcomes across diverse cyber‑physical environments.
Partner with ISC2 to build a more resilient cyber team that can secure the future of IT OT convergence
FAQ: Understanding IT/OT Convergence for Security Leaders
What is it/ot convergence in simple terms?
It/ot convergence means connecting enterprise IT systems with OT systems that monitor or control physical operations so organizations can share data and manage environments more efficiently, while introducing new security and safety considerations.
What are the primary security risks of connecting OT to the internet?
The primary risks include expanded attack surfaces, remote access exposure, identity and credential abuse, and the difficulty of applying standard IT controls to legacy or safety‑critical OT assets.
How does IT/OT convergence impact regulatory compliance (like NIS2)?
Convergence can broaden the scope of systems considered essential to service delivery, increasing expectations for risk management, incident preparedness, supplier assurance and governance across both IT and OT domains.
Which ISC2 certification is best for securing critical infrastructure?
The best ISC2 certification choice depends on role: leaders often need broad governance and risk capability, while practitioners need operational security skills. Many organizations build layered capability across teams using multiple certifications aligned to responsibilities. Scale excellence with your team with training.
H3: Related Insights:
- Read more in this article looking at cybersecurity’s shift from IT to OT
- ISC2 Zero Trust courses provide learning options for implementing Zero Trust to protect OT and IT systems
- OT Security Challenges