How to reverse the trend of BYOD becoming Bring Your Own Cloud.
There is little argument that cloud technology is both powerful and almost infinitely useful. You can run up powerful systems without vast up-front spending on server hardware; you can cast aside the tasks of keeping server and network kit up-to-date or replacing failed components; the ability to run your world in two distant regions with fail-over capability between the two is built into the service; and you can go from zero to a workable setup in a very short amount of time.
The latter is particularly true for Software as a Service (SaaS) offerings. For example, using an AI-based transcription service to convert video and audio webinars and podcasts into text-based versions that are much easier to search through when writing reports and articles based on them. We all know people who use ChatGPT to write program code, job advertisements and the like, while cloud services like DropBox and other file sharing services make moving data around very simple indeed.
Not the Intended Use
However, there’s a problem: many cloud services are susceptible to misuse – often inadvertent, sometimes not. The main issue is people uploading proprietary, often highly sensitive data to a cloud service. Getting ChatGPT to produce your company accounts or write a medical report on your patients’ data is always a bad idea, because once that data is out there in the cloud you have zero control over it and no guarantee that it won’t be loose on the internet forever.
The benefits of cloud services – value and ease of getting up and running – are also the potential downsides. If you’re not seeing “shadow IT” cloud services gradually starting to creep into the organization, with staff signing up to services without going through the formal IT purchasing process, the chances are you’re not looking hard enough. When (not if) you find these pockets of “Bring Your Own Cloud”, as it’s known, what can you do to fix the problem and stop them multiplying?
Addressing Cloud Creep
Step one is to have clear and disseminated policies that prohibit the transfer of company data outside the organization, except to places and services for which such transfers are formally permitted. Writing a policy doesn’t prevent someone from doing something undesirable, of course, but it’s the essential foundation that underpins everything else you’re going to do.
Next, consider a web filtering product or service, so that you can control the web sites and internet-based services your staff can get to. There are many, many of these on the market from a wide variety of reputable suppliers, and the prevalence means they’re generally not inaccessibly expensive. These systems sit between your users’ browsers and the internet and vet every web page they try to visit, permitting or denying access based on the rules you’ve set. These systems are what companies use to prevent staff from going to SaaS solutions you don’t want them to access. There’s a catch, though: there’s no point installing a web filter on your office network if staff take their laptops home and can access things you don’t want them to get to. So, pick one of the solutions that has an “agent” app on every PC, because the agent will hold a copy of your filtering policy and will block access you want to prohibit no matter where the device is.
The other thing you can do is a bit of basic forensic accountancy. If people around the company are signing up to paid-for cloud services, the chances are they’re claiming the cost from the company, whether it’s on their company card or via a personal expense claim. Work with your finance department and check what’s being charged to the company. Keep in mind that if you’re digging through credit card statements a bit of sleuthing might be required to figure out who the vendors actually are.
This is the foundation of what you can do to stem the rise of BYOC, but we haven’t really discussed whether this is what you want to do. Chances are, after all, that there’s a degree of benefit to at least some of the tools that your users have signed up to without your knowledge. Your desire isn’t to stop your users working, but to ensure that they’re not working with systems you don’t know about and risking breaches of confidentiality and data protection.
An Approach to Addressing BYOC
When you find BYOC, don’t just step in, turn it off and step out again. Take the time to speak with the users who have introduced it and understand what they perceive to be its benefit. The outcome in each case will usually take one of three forms.
First, it may well be that the service just isn’t working as the user hoped or is even giving blatantly wrong answers. Take this real ChatGPT example, for instance:
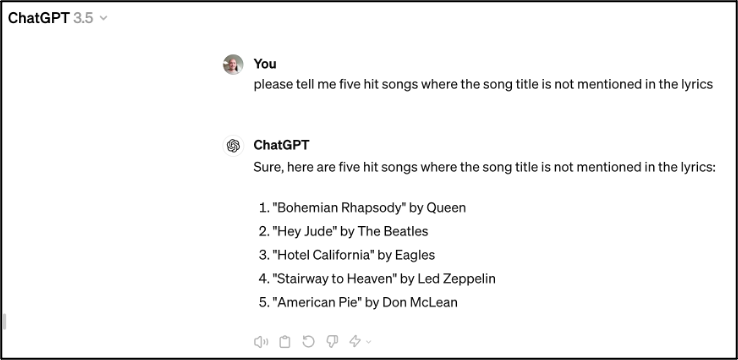
(We particularly like #2, where the song title is in fact the first two words of the first line).
This doesn’t necessarily mean the service isn’t useful, but if it’s not useful for your particular use case then the answer is simply to do away with it.
Option two is that you’ll realize that the service is doing something useful, and seems to be doing it correctly, but that the particular choice of product isn’t ideal. A lot of what you’ll find falls into this category, so consider the value (generally a saving of time and/or cost) and if it’s worth spending time on it, research the alternatives. This is where you might find organizations switching from, for example, ChatGPT to more contained, commercial services like Microsoft’s Copilot. You can ensure the data stays within your subscription rather than being fair game for anyone on the wider internet.
Option three may sound a little surprising: you may well decide that the service the user has signed up to is so valuable and unique that it’s worth considering signing up to it formally as a supported corporate app. You can then go through whatever due-diligence processes are required to on-board the supplier, preferably hook it into your organization’s systems via Single Sign-On (SSO), conduct a proper legal review of the terms and conditions, and so on. Remember: cybersecurity controls should be risk-based, so it may be considered acceptable to adopt a cloud system with some risks by balancing these risks with highly restricted user access and very clear training to maximize awareness of what they can and can’t do. Cybersecurity professionals tend not to like this approach, but don’t dismiss it out of hand.
Bring Your Own Cloud can be a pain and can open you up to cyber breaches or data protection incidents. You simply can’t allow uncontrolled access to arbitrary cloud systems. Nonetheless, don’t be too quick to simply to cut everything off: technology to prevent people from accessing unsupported cloud systems is essential (and, happily, not ferociously expensive), but remember that if someone has signed up to a cloud service, they have probably done it for a reason, and that reason may be one that saves them time and the company money. Fully evaluate what BYOC you have, go and talk to the users, turn off the overly risky stuff. Ultimately, think hard about whether you can work with them to move to something just as beneficial but less risky.
- Find out more about our CCSP certification here
- Cloud Security Skill-Builders grow what you know with short-format learning designed to fit your busy schedule
- Download the CCSP Ultimate Guide here to get everything you need to know about the world’s leading cloud security certification

.png?h=500&iar=0&w=500)

