By: Anindya Chatterjee, CISSP, CCSP
The threat landscape has evolved a lot in the past two years following by the Kaseya incident. With the maturity of software-as-a-service (SaaS) marketplaces and an industry-wide cost saving drive for off the shelf applications, the dependency on managed service providers (MSPs) and application providers has increased.
 Initially, organizations had a choice of on-premise or SaaS deployment but now it’s a decision largely driven by vendor solutions. Organizations are much more dependent on cloud providers and application providers. Today, more that 50 percent of industry applications are bought off-the-shelf and hence the threat pertaining to software supply chain security has increased to an exponential level.
Initially, organizations had a choice of on-premise or SaaS deployment but now it’s a decision largely driven by vendor solutions. Organizations are much more dependent on cloud providers and application providers. Today, more that 50 percent of industry applications are bought off-the-shelf and hence the threat pertaining to software supply chain security has increased to an exponential level.
The global pandemic played a vital role in the evolution of the cyber workplace through the adoption of cloud solutions including desktop-as-a –service (DaaS) and SaaS. Two years ago, the industry was getting to grips with the concepts of trust and untrust, the global pandemic diluted the boundaries and along with it the concept of trust. People were forced to work from home yet remain connected to the office. Patch management, incident management, threat detection and mitigation, which were closed-door activities, now had to be done remotely. Perimeter security controls were no longer effective, and the human emotions of greed and fear peaked.
All these factors working together provide a very fertile land for attackers to distribute and carry forward their activities of exploitation.
What Hasn’t Changed in the Past Few Years?
Organizations have evolved based on a feedback loop of continuous security. However, vendor lock-in and market dominance by key players in the MSP sector still remain a concern. A MSP customer relies on the third-party attestation of the MSP provider without any deep dive knowledge of the effectiveness of the controls. With cloud-based models (private or public) becoming prevalent, the control over Infrastructure security posture is limited. The images used in cloud servers and their patching level still remains a big question. Although there are tools to check and validate, a robust posture management is what the industry needs to focus on.
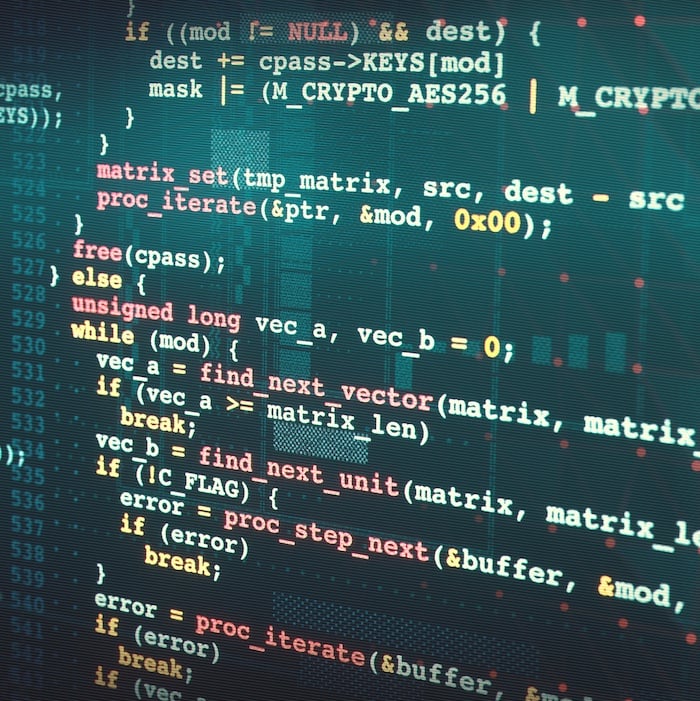
Once a patch is released, or a vulnerability is disclosed, there is always a timeframe before it is applied or else any dependencies and impact can’t be identified. This gap in implementation is always a problem. The threat actors exploit this timeframe and hence the vulnerabilities prevail.
What Is The One Key Learning Opportunity Following the Kaseya Incident?
One key learning from the Kaseya breach is to ensure auto responsiveness exists in the organization security model and includes the same as a part of all supply chain security measures. The IT management tools need to have specific roles and rights identified and accounted for. The learning curve for vulnerabilities needs to be steep for security professionals and the responsiveness for exploits needs to be automated with a review loop in place. With these controls, coupled with people and processes, we can expect attacks of these sort to reduce to a large extent.
This need relies on artificial intelligence (AI) and machine learning (ML) in security for auto notification and incident management. Just like a human immune system, a feedback loop on predictive analysis helps to prevent attacks by reducing the mitigation response time.
What Should Security Teams Prioritize?
Security controls and vulnerabilities are dynamic and so the remediation of the same should also be dynamic. During an incident, priority should be given to identifying and containing in order to reduce the blast radius. Post identification, the testing and release cycle needs to be faster. Pre-identification, a predictive tool kit driven by ML should be able to identify heuristic behaviors and should be able to alert and contain the effected assets.
Security teams need to implement a maturity model for supply chain security. Along with third-party attestation, security teams should have a deep dive knowledge on the remediations and timeframes for fixing key systems and services. Most organizations do look for front-end and back-end controls but what remains neglected is the time taken for closure of a vulnerability.
Whether it’s input from a bug bounty program or a disclosed vulnerability, the resolution timeframe plays a key role in the mitigation and reduction of the blast radius. The quicker this action, the better it is for organizations.
When onboarding vendors or partners, it’s always good to maintain a zero-trust stance. Everything coming from the vendors cannot be trusted and hence the security team needs to be able to analyze traffic patterns and take appropriate actions based on the outcomes. A test environment for patch testing before direct implementation works as a means to contain and analyze an application before widescale deployment.
What should organizations be wary of in terms of future ransomware attacks?
As an analysis of different types of ransomware attacks and their mode of distribution, we can categorize the vectors in two ways. One being the unpatched, unaddressed vulnerabilities and second, and most important, is the weakness in human emotions.
- An up-to-date asset repository with details about patches, operating systems, data types and access is what organizations need to maintain. This will help in identifying the target assets and narrow down the problem to a few rather than going into an unending cycle of discovery at the time of remediation or incident. Patch management, coupled with auto response and remediation with proper testing, is the need of the hour. There is also a concept of virtual patching where a group of assets can be virtually patched at the gateway level until the assets are brought up to date.
- Attackers have always exploited two key human emotions – greed and fear. Organizations need a well planned and executed awareness program to address this. This is a behavior change and hence will need time. It's always good to reach out to the organization concerning fear or greed messages directly from authorized sources rather than believing in email threads or text messages.
We should always remember that the internet has made this world a smaller place. With almost all organizations being present on the internet, it is not difficult to reach out to them through official channels rather than advertisements or messages.
Top three things to be safe from ransomware attacks (direct or indirect):
- Always use licensed and up-to-date version of software. It’s your data so don’t lose control of the systems that handle your data.
- Report and respond immediately. Have checks at the MSP end and also at your end for traffic analysis and response. Predict and prevent by reducing the response time
- Do not trust – It’s your Fear or Greed which is being triggered.
Anindya Chatterjee, CISSP, CCSP, DCPLA is a Cyber Security consultant with 16+ years of experience in Consulting with IT, Telecom, Banking, financial services and insurance Industry.